5 Cybersecurity Tips To Manage Your Remote Personnel Challenges
Did you know that your company’s information can unintentionally be put at risk by you and your employees when working remotely? This could possibly lead to fraud, data breaches, and a plethora of other unwanted consequences.
Although remote working offers many benefits, it also comes with some risks. Continue reading if you want to learn more about the benefits, risks, and ways to lessen a breach as well as tips on how to mitigate one. Learn tips to ensure that cybersecurity is front and center for your workforce.
The Remote Workforce — Is This a New Trend?
Although the world seems to be opening up, many people have gotten comfortable with the new work-from-home trend. So much so that 70% of the global population is working remotely at least once a week. It doesn’t matter what title they use:
● eWorkers
● Teleworkers
● Road Warriors
● Digital Nomads
● Telecommuters
● Remote Workers
● Off-site Employees
One thing is for certain, and two things are for sure, remote workers are here to stay. If your business intends on taking advantage of this thriving pool of talent that’s working remotely, you will need to make some adjustments to the unparalleled cybersecurity risks that come along with it.
Remote Work — Risks and Benefits
Working remotely does come with its share of benefits, but it also comes with substantial risks to you, your company, and your brand if your network is not up-to-date on cybersecurity measures and gets hacked. One benefit is that you could see a reduction in business expenses. Schedules tend to be more flexible, and you don’t have to leave your home, woo-hoo!
The Remote Endpoint
One risk that businesses have to think about now is the remote endpoint. With cybersecurity being challenging for employers, having the correct tools to lessen the risk is essential. Transitioning to a remote workforce will require remote endpoint management.
Businesses believe that their own remote workers can work in a remote environment while being productive, as long as an approach that includes an effective endpoint management security solution is critical. With SOC services, we can also assist IT administrators in overseeing your company’s:
● Remote Endpoints
● Cloud infrastructure
● Network Security
Did you know that Remote Endpoint Protection and Management is currently a leading priority on an IT administrator’s shortlist? Start with the emergence of client management tools, progressing through enterprise mobility management, including mobile device management. The industry has undergone constant transformations.
One significant issue concerning remote work is cybersecurity threats – which is why it is crucial that your company is equipped with the proper applications for your remote working staff – as well as having protected remote endpoints.
Protect Devices With a Sophisticated Endpoint Security Solution
When it comes to remote work, it’s quite different from working in the office, and it’s more challenging to protect telecommuters. One thing to keep in mind is that even though your employee is remote, the same cannot be said about your network. Once your employee clocks/logs in, attackers can enter your network and cause havoc.
Once logged in, your stored documents are at risk because you’re connected to your company’s network. By implementing policies that guarantee that your remote staff has a trustworthy security solution. For instance, with an endpoint security tool by AVG, you can facilitate the prevention of a cyber incident from occurring. It is also essential that the utilized endpoint security solution interacts with remote endpoints that render a thorough endpoint detection and response (EDR) module.
Five Cybersecurity Tips For Your Remote Personnel
1. What Are Some Features of An Endpoint Security Solution?
Real-Time Antivirus Scanning
Antivirus software identifies malware on your computer with active scanning functionality that consistently checks your computer for intrusion from malicious threats.
Behavioral Analysis
The endpoint security solution ought to possess vigorous behavioral analysis functionality. When dealing with malicious executables, you need to understand that they are configured to misdirect security, so behavioral analysis on new executables must be performed securely.
Detection Exploitation
Many of the applications and platforms that you use regularly for work could be harboring hidden threats. Many applications can have vulnerabilities, so make sure that your endpoint security has an exploit detection module.
Endpoint Detection and Response (EDR)
System admins are unable to queue themselves pending team member logins for manual deletion requests. Therefore, it’s critical that when scanning for malware and viruses, any compromised endpoint be secluded. Your endpoint security solution must possess a full EDR module that permits your administrators to remotely:
● Mitigate infection
● Isolate endpoints
● Conduct Forensics
Check out Managed Crowdstrike
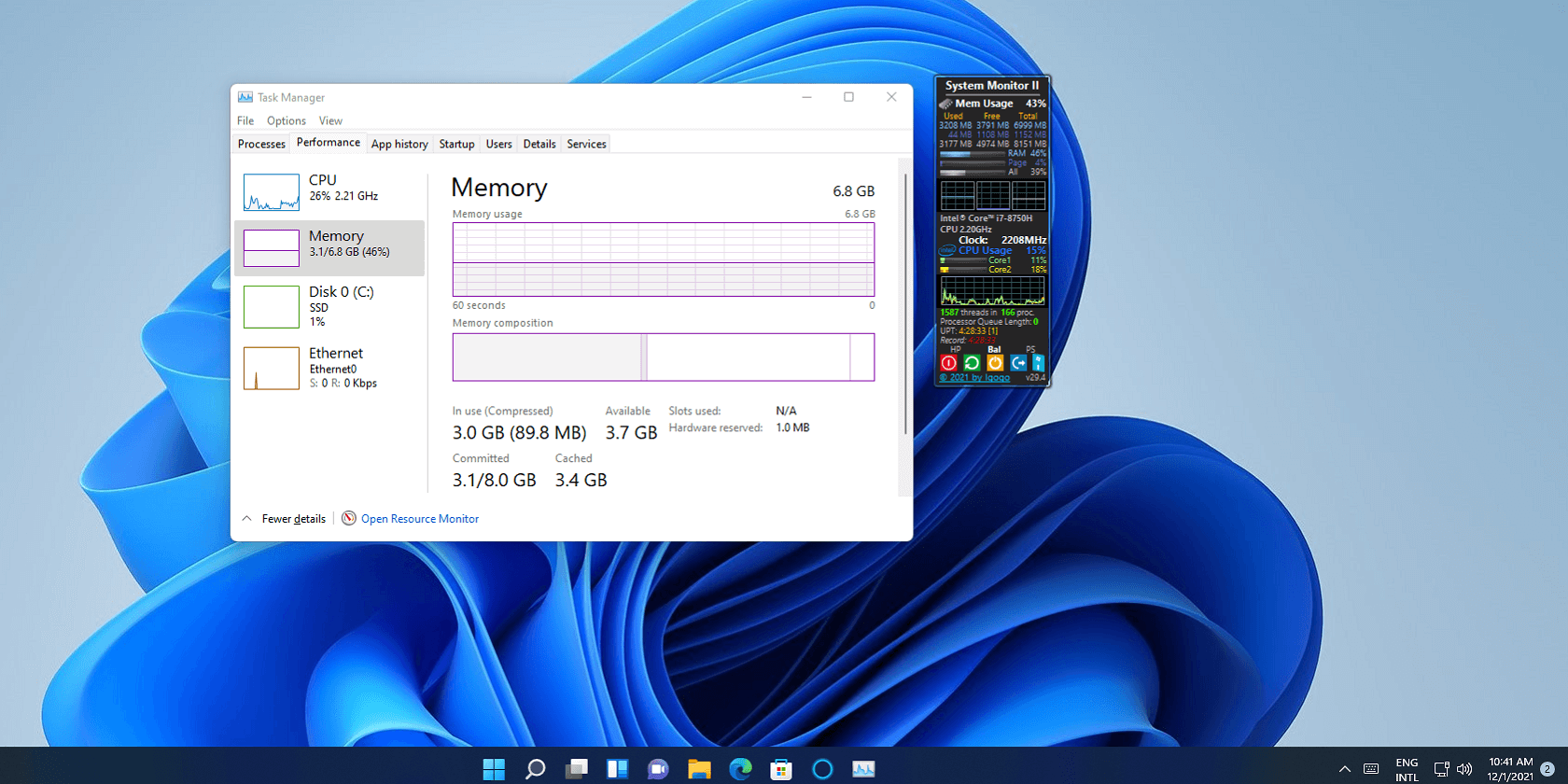
2. Maintain Operating Systems and Program Updates
One of the greatest vulnerabilities is operating systems and applications, which are repeatedly being found and exploited by cybercriminals. Once they’ve gained access, they infiltrate your devices and networks and exploit your personal data.
Remote workers should regularly conduct updates to guarantee that required patches are applied.
3. Set Wi-Fi Configuration Encryption
It is pivotal that you remind your remote workers to configure their Wi-Fi encryption, since you (the employer) do not have complete control of it. It is the employers’ responsibility to ensure that their remote employees are hooked to the internet via an adequately configured Wi-Fi point.
For instance, your home router was probably not set up with a unique password, rather it’s likely using the default password issued by the manufacturer.
Hackers can use this vulnerability to hijack your traffic by hard-coding those default passwords and turning them into malicious software. Remote workers should also change their passwords regularly and use a virtual private network (VPN) to connect to your workplace network when working in a public place.
Proxies can also be used as an additional security measure to protect remote workers’ internet connection. They act as an intermediary between the user and the internet, encrypting all traffic and hiding the user’s IP address from potential hackers.
If you’re interested in using proxies to protect your remote workers’ internet connection, there are many free proxy lists available online that you can try out. However, it’s important to choose a reputable provider and exercise caution when using any online service.
4. For Email and Messaging — Use Corporate Services
Make sure that your remote workers have access to the company’s tools and IT services to assist in maintaining network security. When employees utilize tools, applications, and email for sharing work-related data, it, can assure that your company’s data is secure.
You should also consider a remote worker’s security policy, which will also deem your network more secure.
5. Remain Vigilant
Hacker techniques are evolving daily, as they are relentless. Remind remote employees that they should not click on email attachments or links that they’re not familiar with, and to be mindful of their cyber environment.
Final Thoughts
A pint of prevention is worth a quart of cure. Although working remotely does provide benefits to your employees, it also brings quite a high level of risk to your company. Train your employees on cybersecurity threats regularly to keep your business safe online.
Popular Post
Recent Post
Supercharge Your Productivity: A Solopreneur’s and SMB’s Guide to Mastering Google Workspace with Gemini’
Picture this. It’s Monday morning. You open your laptop. Email notifications flood your screen. Your to-do list has 47 items. Three clients need proposals by Friday. Your spreadsheet crashed yesterday. The presentation for tomorrow’s meeting is half-finished. Sound familiar? Most small business owners live this reality. They jump between apps. They lose files. They spend […]
9 Quick Tips: How To Optimize Computer Performance
Learn how to optimize computer performance with simple steps. Clean hard drives, remove unused programs, and boost speed. No technical skills needed. Start today!
How To Speed Up My Computer/Laptop Windows 11/10 [2025]
Want to make your computer faster? A slow computer can be really annoying. It takes up your time and makes work more difficult. But with a few easy steps, you can improve your laptop’s speed and make things run more smoothly. Your computer slows down over time. Old files pile up. Programs start with Windows. […]
How To Fix Low Disk Space Error Due To A Full Temp Folder
A low disk space error due to a full temp folder is a common problem. Many users face this issue daily. Your computer stores temporary files in special folders. These files ensure optimal program performance, but they can accumulate as time goes on. When temp folders get full, your system slows down. You might see […]
How to Use Disk Cleanup on This Computer: Step-by-Step Guide
Computers getting slow is just the worst, right? Well, yes! Files pile up on your hard drive. Luckily, the Disk Cleanup tool on your PC is here to save the day. It clears out unnecessary files, giving your system the boost it needs to run smoothly again. A lot of users aren’t aware of the […]
Top 25 Computer Maintenance Tips: Complete Guide [2025]
Computer maintenance tips are vital for every PC user. Without proper PC maintenance, your system will slow down. Files can get lost. Programs may crash often. These computer maintenance tips will help you avoid these problems. Good PC maintenance keeps your computer running fast. It makes your hardware last longer. Regular computer maintenance tips can […]
Reclaiming Disk Space On Windows Without Losing Files: A Complete Guide
Running low on storage can slow down programs and trigger that annoying “low disk space” warning. Files accumulate over time, cluttering the drive. The good news? It’s possible to reclaim space without deleting anything important. Reclaiming disk space on Windows without losing files is easier than you think. Your computer stores many temporary files, old […]
Fix Issues Downloading From the Microsoft Store on Windows 11, 10 PC
Do you get excited when you’re about to download a new app or game? You open the Microsoft Store, click the download button… but nothing happens. Or maybe it starts and then suddenly stops. Sometimes, strange messages pop up like “Something happened on our end” or “Try again later.” That can be really annoying. But […]
Fix Low Disk Space Errors Quickly On Windows 11, 10 PC [2025]
Low disk space errors can slow down your Windows PC. These errors appear when your hard drive runs out of room. Your computer needs space to work properly. When space runs low, programs crash and files won’t save. Windows shows warning messages about low disk space. Your PC may freeze or run slowly. You might […]
How To Uninstall Software From My Computer: Complete Guide [2025]
Learning how to uninstall software from my computer is a key skill. Every PC user needs to know this. Old programs take up space. They slow down your system. Unused software creates clutter. When you remove a program from computer, you free up storage. Your PC runs faster. You also fix issues caused by bad […]